Cybersecurity researchers have disclosed particulars of a now-patched vulnerability within the in style figma-developer-mcp Mannequin Context Protocol (MCP) server that might permit attackers to attain code execution.
The vulnerability, tracked as CVE-2025-53967 (CVSS rating: 7.5), is a command injection bug stemming from the unsanitized use of consumer enter, opening the door to a state of affairs the place an attacker can ship arbitrary system instructions.
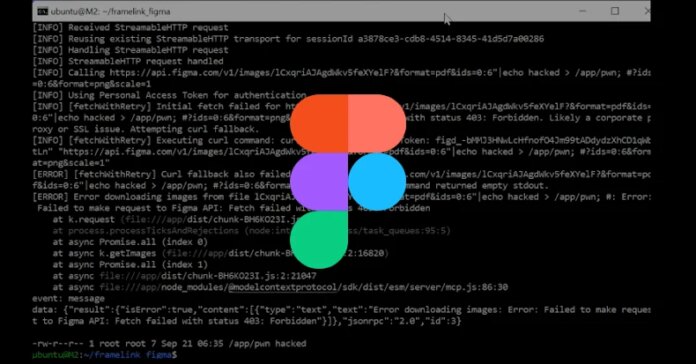
“The server constructs and executes shell instructions utilizing unvalidated consumer enter instantly inside command-line strings. This introduces the opportunity of shell metacharacter injection (|, >, &&, and so forth.),” in keeping with a GitHub advisory for the flaw. “Profitable exploitation can result in distant code execution below the server course of’s privileges.”
Provided that the Framelink Figma MCP server exposes numerous instruments to carry out operations in Figma utilizing synthetic intelligence (AI)-powered coding brokers like Cursor, an attacker might trick the MCP shopper to execute unintended actions via an oblique immediate injection.

Cybersecurity firm Imperva, which found and reported the issue in July 2025, described CVE-2025-53967 as a “design oversight” within the fallback mechanism that might permit dangerous actors to attain full distant code execution, placing builders liable to information publicity.
The command injection flaw “happens throughout the development of a command-line instruction used to ship visitors to the Figma API endpoint,” security researcher Yohann Sillam stated.
The exploitation sequence takes place over by means of steps –
- The MCP shopper sends an Initialize request to the MCP endpoint to obtain an mcp-session-id that is utilized in subsequent communication with the MCP server
- The shopper sends a JSONRPC request to the MCP server with the strategy instruments/name to name instruments like get_figma_data or download_figma_images
The problem, at its core, resides in “src/utils/fetch-with-retry.ts,” which first makes an attempt to get content material utilizing the usual fetch API and, if that fails, proceeds to executing curl command through child_process.exec — which introduces the command injection flaw.

“As a result of the curl command is constructed by instantly interpolating URL and header values right into a shell command string, a malicious actor might craft a specifically designed URL or header worth that injects arbitrary shell instructions,” Imperva stated. “This might result in distant code execution (RCE) on the host machine.”
In a proof-of-concept assault, a distant dangerous actor on the identical community (e.g., a public Wi-Fi or a compromised company machine) can set off the flaw by sending the collection of requests to the weak MCP. Alternatively, the attacker might trick a sufferer into visiting a specifically crafted website as a part of a DNS rebinding assault.
The vulnerability has been addressed in model 0.6.3 of figma-developer-mcp, which was launched on September 29, 2025. As mitigations, it is advisable to keep away from utilizing child_process.exec with untrusted enter and swap to child_process.execFile that eliminates the chance of shell interpretation.
“As AI-driven improvement instruments proceed to evolve and achieve adoption, it is important that security concerns hold tempo with innovation,” the Thales-owned firm stated. “This vulnerability is a stark reminder that even instruments meant to run domestically can turn out to be highly effective entry factors for attackers.”

The event comes as FireTail revealed that Google has opted to not repair a brand new ASCII smuggling assault in its Gemini AI chatbot that may very well be weaponized to craft inputs that may slip by means of security filters and induce undesirable responses. Different massive language fashions (LLMs) vulnerable to this assault are DeepSeek and xAI’s Grok.
“And this flaw is especially harmful when LLMs, like Gemini, are deeply built-in into enterprise platforms like Google Workspace,” the corporate stated. “This system permits automated id spoofing and systematic information poisoning, turning a UI flaw into a possible security nightmare.”