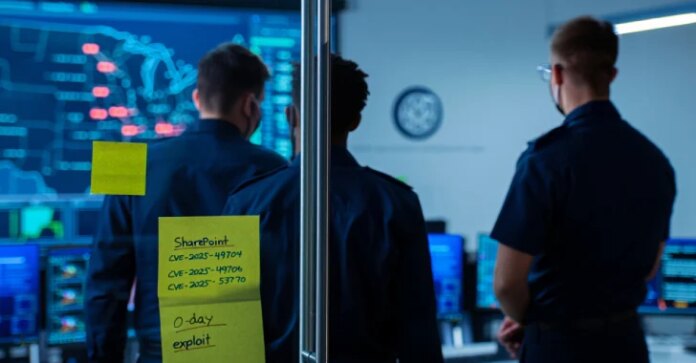
The U.S. Cybersecurity and Infrastructure Safety Company (CISA), on July 22, 2025, added two Microsoft SharePoint flaws, CVE-2025-49704 and CVE-2025-49706, to its Recognized Exploited Vulnerabilities (KEV) catalog, based mostly on proof of lively exploitation.
To that finish, Federal Civilian Government Department (FCEB) companies are required to remediate recognized vulnerabilities by July 23, 2025.
“CISA is conscious of lively exploitation of a spoofing and RCE vulnerability chain involving CVE-2025-49706 and CVE-2025-49704, enabling unauthorized entry to on-premise SharePoint servers,” the company mentioned in an up to date advisory.

The inclusion of the 2 shortcomings, a spoofing vulnerability and a distant code execution vulnerability collectively tracked as ToolShell, to the KEV catalog comes after Microsoft revealed that Chinese language hacking teams like Linen Storm and Violet Storm leveraged these flaws to breach on-premises SharePoint servers since July 7, 2025.
As of writing, the tech big’s personal advisories solely checklist CVE-2025-53770 as being exploited within the wild. What’s extra, it describes the 4 flaws as under –
- CVE-2025-49704 – SharePoint Distant Code Execution
- CVE-2025-49706 – SharePoint Publish-auth Distant Code Execution
- CVE-2025-53770 – SharePoint ToolShell Authentication Bypass and Distant Code Execution
- CVE-2025-53771 – SharePoint ToolShell Path Traversal
The truth that CVE-2025-53770 is each an authentication bypass and a distant code execution bug signifies that CVE-2025-53771 will not be crucial to construct the exploit chain. CVE-2025-53770 and CVE-2025-53771 are assessed to be patch bypasses for CVE-2025-49704 and CVE-2025-49706, respectively.
“The basis trigger [of CVE-2025-53770] is a mixture of two bugs: An authentication bypass (CVE-2025-49706) and an insecure deserialization vulnerability (CVE-2025-49704),” the Akamai Safety Intelligence Group mentioned.
When reached for remark concerning the exploitation standing of CVE-2025-53771 and different flaws, a Microsoft spokesperson advised The Hacker Information that the knowledge revealed in its advisories is right “on the time of unique publication” and that it doesn’t sometimes replace post-release.
“Microsoft additionally assists CISA with the Recognized Exploited Vulnerabilities Catalog which offers commonly up to date data on exploited vulnerabilities,” the spokesperson added.

The event comes as watchTowr Labs advised the publication that it has internally devised a way exploiting CVE-2025-53770 such that it bypasses Antimalware Scan Interface (AMSI), a mitigation step outlined by Microsoft to forestall unauthenticated assaults.
“This has allowed us to proceed figuring out weak methods even after mitigations like AMSI have been utilized,” watchTowr CEO Benjamin Harris mentioned. “AMSI was by no means a silver bullet, and this end result was inevitable. However we’re involved to listen to that some organizations are selecting to ‘allow AMSI’ as an alternative of patching. This can be a very dangerous concept.”
“Now that exploitation has been linked to nation-state actors, it could be naive to suppose they might leverage a SharePoint zero-day however in some way not bypass AMSI. Organizations should patch. Ought to go with out saying – all the general public PoCs will set off AMSI, and mislead organizations into believing the mitigations are complete/the host is not weak. This could be incorrect.”