Even in well-secured environments, attackers are getting in—not with flashy exploits, however by quietly making the most of weak settings, outdated encryption, and trusted instruments left unprotected.
These assaults do not rely on zero-days. They work by staying unnoticed—slipping via the cracks in what we monitor and what we assume is protected. What as soon as regarded suspicious now blends in, because of modular strategies and automation that duplicate regular habits.
The actual concern? Management is not simply being challenged—it is being quietly taken. This week’s updates spotlight how default settings, blurred belief boundaries, and uncovered infrastructure are turning on a regular basis methods into entry factors.
⚡ Risk of the Week
Important SharePoint Zero-Day Actively Exploited (Patch Launched As we speak) — Microsoft has launched fixes to deal with two security flaws in SharePoint Server which have come beneath lively exploitation within the wild to breach dozens of organizations the world over. Particulars of exploitation emerged over the weekend, prompting Microsoft to challenge an advisory for CVE-2025-53770 and CVE-2025-53771, which at the moment are assessed to be patch bypasses for 2 different SharePoint flaws tracked as CVE-2025-49704 and CVE-2025-49706, an exploit chain dubbed ToolShell that might be leveraged to attain distant code execution on on-premises SharePoint servers. The 2 vulnerabilities had been addressed by Microsoft earlier this month as a part of its Patch Tuesday replace. It is presently not identified who’s behind the mass-exploitation exercise.
🔔 High Information
- Google Ships Patch for Actively Exploited Chrome Flaw — Google out patches to resolve a high-severity vulnerability in Chrome browser (CVE-2025-6558) that has come beneath lively exploitation within the wild, making it the fifth zero-day to be both actively abused or demonstrated as a proof-of-concept (PoC) for the reason that begin of the 12 months. The vulnerability is an incorrect validation of untrusted enter within the browser’s ANGLE and GPU parts that would permit an attacker to doubtlessly carry out a sandbox escape by way of a crafted HTML web page. The difficulty has been addressed in variations 138.0.7204.157/.158 for Home windows and Apple macOS, and 138.0.7204.157 for Linux.
- Important NVIDIA Container Toolkit Flaw Disclosed — A vital vulnerability in NVIDIA Container Toolkit (CVE-2025-23266) might be exploited to attain code execution with elevated permissions. “A profitable exploit of this vulnerability would possibly result in escalation of privileges, information tampering, info disclosure, and denial-of-service,” the GPU maker mentioned. Wiz, which disclosed the flaw, mentioned the shortcoming might be trivially exploited to entry, steal, or manipulate the delicate information and proprietary fashions of all different clients operating on the identical shared {hardware} by way of a three-line exploit.
- New CrushFTP Bug Comes Underneath Attack — CrushFTP revealed {that a} vital flaw in its file switch software program (CVE-2025-54309) has been exploited within the wild, with unknown menace actors reverse engineering its supply code to find the bug and goal gadgets which might be but to be up to date to the newest variations. The difficulty impacts all variations of CrushFTP 10 earlier than 10.8.5 and 11 earlier than 11.3.4_23. “The assault vector was HTTP(S) for the way they might exploit the server,” CrushFTP mentioned. “We had fastened a unique challenge associated to AS2 in HTTP(S) not realizing {that a} prior bug might be used like this exploit was. Hackers apparently noticed our code change, and discovered a technique to exploit the prior bug.”
- Golden dMSA Attack in Home windows Server 2025 Permits Cross-Area Attacks — Cybersecurity researchers disclosed a “vital design flaw” in delegated Managed Service Accounts (dMSAs) launched in Home windows Server 2025 that would allow cross-domain lateral motion and chronic entry to all managed service accounts and their assets throughout Energetic Listing indefinitely. “The assault leverages a vital design flaw: A construction that is used for the password-generation computation incorporates predictable time-based parts with only one,024 doable mixtures, making brute-force password era computationally trivial,” Semperis researcher Adi Malyanker mentioned.
- Google Large Sleep AI Agent Flags Important SQLite Flaw Earlier than Exploitation — Large Sleep, a man-made intelligence (AI) agent launched by Google final 12 months as a collaboration between DeepMind and Google Undertaking Zero, facilitated the invention of a vital security flaw in SQLite (CVE-2025-6965) that was beforehand solely identified to attackers as a zero-day and was on the verge of exploitation. Google described it as the primary time an AI agent has been used to “straight foil efforts to use a vulnerability within the wild.”
- Risk Actors Goal EoL SonicWall SMA 100 Gadgets — Unknown intruders codenamed UNC6148 are focusing on absolutely patched end-of-life SonicWall Safe Cellular Entry (SMA) 100 collection home equipment and deploying a novel, persistent backdoor and rootkit referred to as OVERWATCH. Many key particulars in regards to the marketing campaign are presently unknown. For starters, Google mentioned it doesn’t have sufficient information to find out the place the menace actors are primarily based, or what their motives are. Second, the assaults are exploiting leaked native administrator credentials on the focused gadgets for preliminary entry. But it surely has been unable to pinpoint how the attackers managed to acquire the credentials used within the assault. Whereas it is doable that they had been sourced from infostealer logs or credential marketplaces, the corporate famous it is extra doubtless that the attackers leveraged a identified vulnerability. It is also unclear exactly what the attackers are attempting to perform after they take management of a tool. The lack of awareness largely stems from how OVERWATCH features, which permits the attackers to selectively take away log entries to hinder forensic investigation. The investigation additionally discovered that UNC6148 additionally managed to deploy a reverse shell on contaminated gadgets, one thing that ought to not usually be doable, resulting in speculations {that a} zero-day may need been in play. The findings as soon as once more present community home equipment are widespread attacker targets, as they provide a technique to achieve entry to high-value networks.
️🔥 Trending CVEs
Hackers are fast to leap on newly found software program flaws – generally inside hours. Whether or not it is a missed replace or a hidden bug, even one unpatched CVE can open the door to critical injury. Under are this week’s high-risk vulnerabilities making waves. Overview the record, patch quick, and keep a step forward.
This week’s record contains — CVE-2025-53770, CVE-2025-53771 (Microsoft SharePoint Server), CVE-2025-37103 (HPE On the spot On Entry Factors), CVE-2025-54309 (CrushFTP), CVE-2025-23266, CVE-2025-23267 (NVIDIA Container Toolkit), CVE-2025-20337 (Cisco Identification Companies Engine and ISE Passive Identification Connector), CVE-2025-6558 (Google Chrome), CVE-2025-6965 (SQLite), CVE-2025-5333 (Broadcom Symantec Endpoint Administration Suite), CVE-2025-6965 (SQLite), CVE-2025-48384 (Git CLI), CVE-2025-4919 (Mozilla Firefox), CVE-2025-53833 (LaRecipe), CVE-2025-53506 (Apache Tomcat), CVE-2025-41236 (Broadcom VMware ESXi, Workstation, and Fusion), CVE-2025-27210, CVE-2025-27209 (Node.js), CVE-2025-53906 (Vim), CVE-2025-50067 (Oracle Utility Categorical), CVE-2025-30751 (Oracle Database), CVE-2025-6230, CVE-2025-6231, CVE-2025-6232 (Lenovo Vantage), CVE-2024-13972, CVE-2025-7433, CVE-2025-7472 (Sophos Intercept X for Home windows), CVE-2025-27212 (Ubiquiti UniFi Entry), CVE-2025-4657 (Lenovo Safety Driver), CVE-2025-2500 (Hitachi Power Asset Suite), CVE-2025-6023, CVE-2025-6197 (Grafana), CVE-2025-40776, CVE-2025-40777 (BIND 9), CVE-2025-33043, CVE-2025-2884, CVE-2025-3052 (Gigabyte), and CVE-2025-31019 (Password Coverage Supervisor plugin).
📰 Across the Cyber World
- Russian Sentenced to three Years in Jail within the Netherlands for Sharing Data — A Rotterdam courtroom sentenced a 43-year-old Russian to 3 years in jail for breaching worldwide sanctions by sharing delicate ASML info from Dutch semiconductor chip machine maker ASML and NXP with an individual in Russia. At his trial on June 26, the suspect admitted to copying recordsdata final 12 months and sending them to an individual in Russia utilizing the Sign messaging app. Whereas the identify of the defendant was not disclosed, Reuters reported in February 2025 that the perpetrator was German Aksenov, and that he had contact with Russia’s FSB intelligence service. He was charged with IP theft and sanctions violations in December 2024.
- U.Okay. NCSC Launches Vulnerability Analysis Initiative — The U.Okay. Nationwide Cyber Safety Centre (NCSC) introduced a brand new Vulnerability Analysis Initiative (VRI) that goals to strengthen relations with exterior cybersecurity consultants. “The VRI’s mission is to strengthen the UK’s means to hold out VR,” the NCSC mentioned. “We work with the most effective exterior vulnerability researchers to ship a deep understanding of security on a variety of applied sciences we care about. The exterior VRI group additionally helps us in having instruments and tradecraft for vulnerability discovery.”
- Storm-1516 Spreads Disinformation in Europe — A Kremlin-linked disinformation group tracked as Storm-1516 has been masquerading as actual journalists and publishing pretend articles on spoofed information web sites to unfold false narratives in France, Armenia, Germany, Moldova, and Norway. The menace actors used the names and pictures of respectable reporters to lend credibility to the bogus articles, per the Gnida Undertaking. One other pro-Russia disinformation marketing campaign referred to as Operation Overload (aka Matryoshka or Storm-1679) has been noticed leveraging consumer-grade synthetic intelligence instruments to gasoline a “content material explosion” centered round exacerbating current tensions round international elections, Ukraine, and immigration, amongst different controversial points. The exercise, working since 2023, has a monitor document of disseminating false narratives by impersonating media shops with the obvious intention of sowing discord in democratic international locations. “This marks a shift towards extra scalable, multilingual, and more and more refined propaganda techniques,” Reset Tech and Verify First mentioned. “The marketing campaign has considerably amped up the manufacturing of recent content material prior to now eight months, signalling a shift towards sooner, extra scalable content material creation strategies.” Among the pictures used within the marketing campaign are believed to have been generated utilizing Flux AI, a text-to-image generator developed by Black Forest Labs. The corporate informed WIRED that it has constructed “a number of layers of safeguards” to forestall abuse and that it is dedicated to working with social media platforms and authorities to push back illegal misuse.
- SLOW#TEMPEST Marketing campaign’s Evolving Strategies Detailed — The menace actors behind a malware marketing campaign referred to as SLOW#TEMPEST have been noticed utilizing DLL-sideloading strategies to launch a malicious DLL, whereas counting on Management Movement Graph (CFG) obfuscation and dynamic perform calls to hide the code within the loader DLL. The first purpose of the DLL is to unpack and launch an embedded payload straight in reminiscence provided that the goal machine has at the least 6 GB of RAM. “The SLOW#TEMPEST marketing campaign’s evolution highlights malware obfuscation strategies, particularly dynamic jumps and obfuscated perform calls,” Palo Alto Networks Unit 42 mentioned. “The success of the SLOW#TEMPEST marketing campaign utilizing these strategies demonstrates the potential affect of superior obfuscation on organizations, making detection and mitigation considerably more difficult.”
- Abacus Market Shutters After Seemingly Exit Rip-off — The darknet market referred to as Abacus Market has all of the sudden closed its operations, rendering all its infrastructure, together with its clearnet mirror, inaccessible. The event comes after Abacus Market customers started reporting withdrawal points in late June 2025. Blockchain intelligence agency TRM Labs mentioned {the marketplace}’s creators could have probably pulled off an exit rip-off and disappeared with customers’ funds, though the opportunity of a legislation enforcement seizure hasn’t been dominated out. Abacus’s exit follows the June 16, 2025, seizure of Archetyp Market by Europol. Abacus Market launched in September 2021 as Alphabet Market, earlier than it rebranded to its present identify two months later. {The marketplace} is estimated to have generated wherever between $300 million and $400 million in cryptocurrency gross sales, spanning illicit medication, counterfeit gadgets, and stolen playing cards. In line with information from Chainlysis, Abacus Market’s income has elevated considerably, rising by 183.2% YoY in 2024.
- MITRE Broadcasts AADAPT for Cryptocurrency Safety — The MITRE Company launched Adversarial Actions in Digital Asset Cost Applied sciences, aka AADAPT, a cybersecurity framework for addressing vulnerabilities in digital monetary methods comparable to cryptocurrency. It is modeled after the MITRE ATT&CK framework. “AADAPT offers builders, policymakers, and monetary organizations with a structured methodology for figuring out, analyzing, and mitigating potential dangers related to digital asset funds,” MITRE mentioned. “By utilizing insights derived from real-world assaults as cited by greater than 150 sources from authorities, trade, and academia, the AADAPT framework identifies adversarial techniques, strategies, and procedures linked to digital asset fee applied sciences, together with consensus algorithms and sensible contracts.”
- U.S. Ex-Military soldier Pleads Responsible to Hacking 10 Telcos — Former U.S. Military soldier Cameron John Wagenius (aka kiberphant0m and cyb3rph4nt0m) pleaded responsible to hacking and extorting at the least 10 telecommunications corporations between April 2023 and December 2024. The 21-year-old “conspired with others to defraud at the least 10 sufferer organizations by acquiring login credentials for the organizations’ protected pc networks,” the U.S. Division of Justice (DoJ) mentioned. “The conspirators obtained these credentials utilizing a hacking software that they referred to as SSH Brute, amongst different means. They used Telegram group chats to switch stolen credentials and focus on gaining unauthorized entry to sufferer corporations’ networks.” The menace actors behind the scheme then extorted the sufferer organizations each privately and on cybercrime boards comparable to BreachForums and XSS.is by providing to promote the stolen information for 1000’s of {dollars}. Among the information was finally bought and used to perpetuate different frauds, together with SIM-swapping. Wagenius et al are mentioned to have tried to extort at the least $1 million from sufferer information homeowners. The assaults happened whereas Wagenius was on lively obligation, the DoJ mentioned. Courtroom paperwork present that the defendant Googled for phrases like “can hacking be treason” and “U.S. navy personnel defecting to Russia.” In February 2025, Wagenius pleaded responsible to conspiracy to commit wire fraud, extortion in relation to pc fraud, aggravated identification theft, and illegal switch of confidential telephone data info. He’s scheduled for sentencing on October 6, 2025. His alleged co-conspirators, Connor Moucka and John Binns, had been indicted in November 2024.
- Signed Drivers in Malicious Campaigns — Since 2020, a minimum of 620 signed drivers, 80 certificates, and 60 Home windows {Hardware} Compatibility Program (WHCP) accounts have been related to menace actor campaigns. The vast majority of drivers have been signed by 131 Chinese language corporations. In 2022 alone, over 250 drivers and roughly 34 certificates and WHCP accounts had been recognized as doubtlessly compromised. The findings present that “kernel-level assaults stay extremely enticing to menace actors regardless of Microsoft’s improved defenses, as a result of highest degree of privileges on the compromised system and management they provide to attackers,” Group-IB mentioned, including it discovered overlap within the signing infrastructure throughout totally different malware campaigns, comparable to these utilizing POORTRY and RedDriver. Among the notable malware strains utilizing kernel loaders for added stealth embody Festi, FiveSys, FK_Undead, and BlackMoon. “Attackers leverage many signing certificates and WHCP accounts by exploiting respectable processes just like the WHCP and Prolonged Validation (EV) certificates. This contains these belonging to compromised or fraudulently registered organizations, signing malicious drivers, bypassing established security measures, and exploiting the belief mannequin inherent in signed kernel drivers,” the corporate famous.
- TeleMessage SGNL Flaw Seeing Exploitation Exercise — Risk actors are actively making an attempt to use a security flaw in TeleMessage SGNL, an enterprise messaging system modeled after Sign, utilized by authorities companies and enterprises alike to attain safe communications. The vulnerability, CVE-2025-48927, can be utilized to leak delicate info, together with plaintext usernames, passwords, and different information. In line with GreyNoise, exploitation efforts are coming from 25 IP addresses over the previous 30 days. The vast majority of the IP addresses are from France, adopted by Singapore, Germany, Hong Kong, and India. The assaults goal the USA, Singapore, India, Mexico, and Brazil.
- Microsoft Stops Counting on Chinese language Engineers for Protection Cloud Help — Microsoft modified its practices to make sure that engineers in China not present technical help to U.S. protection shoppers utilizing the corporate’s Azure cloud providers. The revamps got here after a ProPublica investigation revealed that Microsoft has been utilizing Chinese language engineers to assist preserve U.S. Division of Protection methods, doubtlessly exposing delicate information to the Chinese language authorities. “In response to issues raised earlier this week about US-supervised overseas engineers, Microsoft has made adjustments to our help for US Authorities clients to guarantee that no China-based engineering groups are offering technical help for DoD Authorities cloud and associated providers,” the corporate mentioned.
- Japan Authorities Launch Free Phobos and 8Base Decryptor — Japan’s Nationwide Police Company printed a free decryption software and a information in English for organizations impacted by the Phobos and 8Base ransomware assaults. Earlier this February, two Russian nationals accused of utilizing the Phobos ransomware to assault greater than 1,000 entities had been charged as a part of a world legislation enforcement takedown. Phobos launched in December 2018, with a modified model referred to as 8Base gaining prominence in 2023.
- Android Permits Gemini Entry Third-Get together Apps — Google has carried out a change that can permit its Gemini synthetic intelligence (AI) chatbot to work together with different apps put in on Android gadgets, comparable to Cellphone, Messages, and others, even when customers have turned off “Gemini Apps Exercise.” In line with a help doc from the corporate, “Even when Gemini Apps Exercise is off, your conversations might be saved together with your account for as much as 72 hours. This lets Google present the service and course of any suggestions. This exercise will not seem in your Gemini Apps Exercise.” The replace went into impact this month.
- EvilPanel Phishing Toolkit Detailed — Cybersecurity researchers have found a brand new phishing toolkit referred to as EvilPanel that is constructed on Evilginx and offers an internet interface for launching multi-factor authentication (MFA)-bypassing assaults. “EvilPanel wraps all of Evilginx’s highly effective AiTM capabilities right into a smooth, user-friendly internet interface, eliminating the necessity for handbook configuration and reducing the barrier to entry for would-be attackers,” Irregular AI mentioned. “EvilPanel’s core phishing performance follows the Evilginx mannequin – i.e., it maintains the login circulation by performing as a clear proxy.”
- Katz Stealer and Octalyn Stealer Detailed — Cybersecurity firm SentinelOne is warning that menace actors are more and more adopting an info stealer referred to as Katz Stealer owing to its “sturdy credential and information discovery with theft capabilities in addition to trendy evasion and anti-analysis options.” It described the stealer as a “mixture of credential theft and trendy malware design.” Provided beneath a Malware-as-a-Service (MaaS) mannequin for a mere $50 per 30 days (or $360 for an entire 12 months), stealers comparable to Katz are turnkey instruments that decrease the barrier to entry for pulling off malicious assaults. A notable characteristic of Katz Stealer is its means to defeat Chromium’s app-bound encryption to realize entry to and extract credentials and cookies. “Katz Stealer will not be a ‘one shot’ infostealer; it’s designed to repeatedly exfiltrate the sufferer’s information,” SentinelOne mentioned. “The malware not solely extracts information discovered on a focused system on the level of an infection but additionally as information up to date, modified, or freshly launched.” One other new stealer masquerades as an academic software referred to as Octalyn Forensic Toolkit, however acts as a credential stealer, harvesting browser information, Discord and Telegram tokens, VPN configurations, gaming accounts, and cryptocurrency pockets artifacts. “Its modular C++ payload, Delphi-based builder, Telegram-based C2, and secondary payload supply functionality make it a potent software for menace actors,” CYFIRMA mentioned. “Using obfuscation, Home windows persistence strategies, and structured information theft highlights a deliberate effort to evade detection and maximize affect.”
- Armenia Passes Use of Facial Recognition Expertise by Police — Armenia’s parliament has handed controversial amendments to the nation’s Regulation on Police, granting the Ministry of Inner Affairs entry to a nationwide community of real-time surveillance cameras which might be geared up with facial recognition expertise. The cameras will function throughout state and municipal buildings, public transport, airports, and parking areas. The legislation is ready to take impact on August 9, 2025. The CSO Meter mentioned the legislation “lacks clear authorized safeguards, public oversight, and correct regulation of synthetic intelligence (AI) applied sciences,” posing a danger to residents’ privateness.
- Scammers Utilizing MaisonReceipts to Create Pretend Receipts — Fraudsters are utilizing instruments like MaisonReceipts to generate counterfeit receipts for over 21 well-known retail manufacturers in a number of currencies (USD, EUR, GBP). They’re utilized by teams that resell counterfeit or stolen gadgets, presenting them as genuine utilizing bogus receipts. “The service is marketed via subscription-based web sites, social media accounts, and encrypted messaging platforms, with options that make the fraudulent receipts seem convincing sufficient to deceive shoppers and on-line marketplaces,” Group-IB mentioned.
- PyPI Blocks inbox.ru Electronic mail Area — A current spam marketing campaign towards PyPI has prompted the maintainers of the Python Bundle Index (PyPI) repository to ban the usage of the “inbox.ru” e-mail area throughout new registrations in addition to including additional e-mail addresses. “The marketing campaign created over 250 new person accounts, publishing over 1,500 new tasks on PyPI, resulting in end-user confusion, abuse of assets, and potential security points,” PyPI mentioned. “All related tasks have been faraway from PyPI, and accounts have been disabled.”
- Silver Fox Actor Creates Pretend Web sites for Malware Supply — The menace actor referred to as Silver Fox, which is understood for focusing on Chinese language-speaking people and entities, has created over 2,800 domains since June 2023, with 266 of the over 850 recognized domains since December 2024 actively distributing malware. These pretend web sites act as a supply vector for Home windows-specific malware and masquerade as utility obtain websites and software program replace prompts. “The constant operational timing throughout all hours with excessive influxes throughout Chinese language working hours, along with different elements, suggests a mixture of automated and certain human-driven method to their actions,” DomainTools mentioned.
- Arrested Scattered Spider Members Launched on Bail — A British courtroom has launched 4 members of the Scattered Spider group on bail. They had been arrested final week on suspicion of Pc Misuse Act offenses, blackmail, cash laundering, and collaborating within the actions of an organized crime group. They have been charged with hacking U.Okay. retailers Marks & Spencer, Co-op, and Harrods.
- Armenian Nationwide Charged with Ryuk Ransomware Attacks — An Armenian man extradited from Ukraine to the USA has been charged over his alleged function in Ryuk ransomware assaults between March 2019 and September 2020. Karen Serobovich Vardanyan was arrested in Kyiv in April, and was extradited to the USA on June 18. Vardanyan has been charged with conspiracy, fraud in reference to computer systems, and extortion in reference to computer systems. He has been charged alongside Levon Georgiyovych Avetisyan, 45, who can also be an Armenian nationwide going through the identical fees. He’s presently detained in France and is predicted to be extradited as properly. Vardanyan and his accomplices acquired about 1,610 bitcoins from victims, valued at greater than $15 million on the time of fee. Two Ukrainians — 53-year-olds Oleg Nikolayevich Lyulyava and Andrii Leonydovich Prykhodchenko — had been additionally charged in reference to Ryuk exercise however stay at giant.
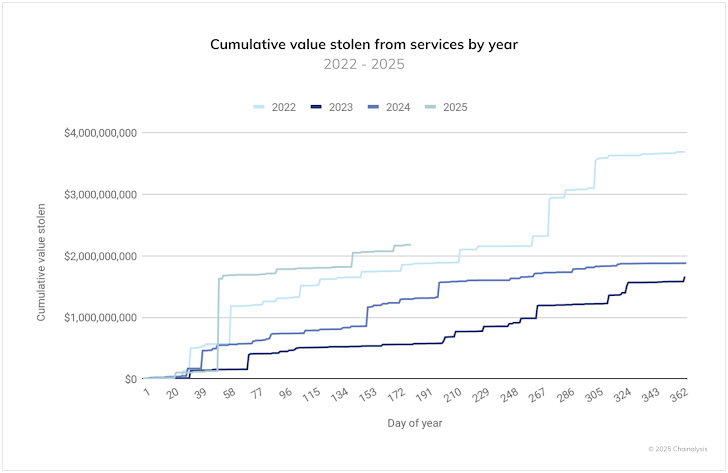
- $2.17B Stolen from Crypto Companies in 2025 — Hackers and scammers have stolen over $2.17 billion in crypto property within the first half of this 12 months, with North Korea’s $1.5 billion hack of Bybit accounting for almost all of the property. Data from TRM Labs exhibits that $2.1 billion was stolen throughout at the least 75 distinct hacks and exploits. A complete of $801,315,669 was misplaced throughout 144 incidents in Q2 2025, per CertiK. Pockets compromise emerged as the costliest assault vector in H1 2025, with $1,706,937,700 stolen throughout 34 incidents. “To date in 2025, important concentrations of stolen fund victims have emerged within the U.S., Germany, Russia, Canada, Japan, Indonesia, and South Korea,” Chainalysis mentioned. “Private pockets compromises make up a rising share of whole ecosystem worth stolen over time.”
- Japan Focused by North Korea and China in 2024 — Japanese organizations have been focused by North Korean menace actors to distribute malware households like BeaverTail, InvisibleFerret, and RokRAT, in addition to by Chinese language hacking teams comparable to Mustang Panda, Stone Panda, MirrorFace, Teleboyi, and UNC5221. The China-linked assaults led to the deployment of backdoors and trojans like ANEL and PlugX, Macnica mentioned.
- Rainbow Hyena Goes After Russian Corporations — The menace actor referred to as Rainbow Hyena focused Russian healthcare and IT organizations utilizing phishing emails containing malicious attachments to distribute a C++-based customized backdoor referred to as PhantomRemote. “The backdoor collects details about the compromised system, hundreds different executables from the C2 server, and runs instructions by way of the cmd.exe interpreter,” BI.ZONE mentioned.
- Migration to Put up-Quantum Cryptography is Uneven — About 6% of all 186 million SSH servers on the web already use quantum-safe encryption, in keeping with a brand new report from Forescout Analysis – Vedere Labs. “Three quarters of OpenSSH variations on the web nonetheless run variations launched between 2015 and 2022 that don’t help quantum-safe encryption,” the corporate mentioned. “If regulators mandate quantum-safe encryption within the close to future, organizations will face critical gaps. Outdated infrastructure will develop into a compliance and security danger.”
- Brazilian Police Arrest IT Employee for $100 Million Cyber Theft — Authorities in Brazil arrested a suspect in reference to a cyber assault that diverted greater than $100 million from the nation’s banking methods. Per a report from Related Press, the suspect has been recognized as João Roque, an IT worker of a software program firm named C&M and he allegedly helped unknown menace actors achieve unauthorized entry to Brazil’s prompt fee system, referred to as PIX, by promoting his credentials to them earlier this 12 months for about $2,700 in two separate money funds. As soon as the cybercriminals breached the corporate’s community, they carried out fraudulent PIX transactions. It is believed that the losses might go up additional, because the loss refers to only one monetary establishment that contracted with C&M.
- Italian Police Arrest Diskstation Ransomware Gang — Italian police have arrested a 44-year-old Romanian for finishing up cyber assaults towards Italian corporations as a part of a legislation enforcement effort referred to as Operation Elicius. The unidentified man is alleged to be the chief of the DiskStation Safety ransomware group, which has focused Synology network-attached storage (NAS) gadgets since 2021. He faces fees of unauthorized entry to pc methods and extortion.
- Samsung Broadcasts KEEP to Retailer Delicate Data — Samsung introduced plenty of security and privateness updates to its Galaxy smartphones with One UI 8, together with help for quantum-resistant Wi-Fi connections utilizing ML‑KEM and a brand new structure referred to as Knox Enhanced Encrypted Safety (KEEP) that creates encrypted, app-specific storage environments for storing information. KEEP additionally integrates with Samsung’s Private Data Engine (PDE) and Knox Vault, the corporate’s {hardware} security surroundings, to allow personalised synthetic intelligence (AI) options by analyzing customers’ information on-device.
- Cambodia Arrests Over 1,000 Amid Crackdown on On-line Scams — Cambodian authorities have arrested greater than 1,000 suspects linked to on-line scams in an effort to crack down on cybercrime operations within the nation. These detained included over 200 Vietnamese, 27 Chinese language, and 75 suspects from Taiwan and 85 Cambodians within the capital Phnom Penh and the southern metropolis of Sihanoukville. About 270 Indonesians, together with 45 ladies, had been arrested in Poipet. In a associated improvement, Thai officers raided properties linked to a Cambodian senator and enterprise tycoon, Kok An, in relation to an area community of cyber rip-off name facilities.
🎥 Cybersecurity Webinars
- From Autofill to Alarm Bells: Securing Identification within the Age of AI — Logins obtained simpler—however belief obtained tougher. As AI reshapes digital identification, customers are questioning how their information is used and who’s actually behind the display. On this session, uncover how high manufacturers are tackling AI-driven identification dangers whereas rebuilding belief with smarter, privacy-first authentication methods.
- How Attackers Hijack Your Dependencies—and What DevSecOps Groups Should Do Now — Your Python surroundings is beneath assault—quietly, and from inside. In 2025, repo hijacks, poisoned packages, and typosquatting aren’t uncommon edge instances—they’re a part of the menace panorama. This webinar exhibits builders and DevSecOps leaders how you can lock down the Python provide chain earlier than compromised dependencies take down your methods.
- Your AI Copilot Might Be Letting Attackers In — Study Lock Down the Identification Layer — AI copilots are boosting productiveness—and attackers are utilizing the identical energy to interrupt your identification perimeter. From API abuse to artificial logins, the identification layer is beneath siege. Be part of Okta to discover ways to safe AI-powered workflows, detect AI-driven threats, and make identification your strongest line of protection in 2025.
🔧 Cybersecurity Instruments
- OSINTMap — It’s a light-weight software that helps you rapidly discover and use widespread OSINT assets. It organizes a whole bunch of investigation hyperlinks—like individuals search, area lookups, and breach checkers—into one easy-to-browse native dashboard. Excellent for anybody doing OSINT work, it saves time by conserving all the things in a single place.
- NortixMail — It’s an open-source, self‑hosted disposable e-mail server that makes burner addresses straightforward—with out the standard e-mail server headache. You possibly can spin it up with Docker or manually, generate short-term e-mail addresses on demand, and consider messages by way of a clear internet interface. Because it retains messages domestically and does not depend on third-party providers, it is an important software for testing, avoiding spam, or defending your inbox throughout dangerous signal‑ups.
Disclaimer: These newly launched instruments are for academic use solely and have not been absolutely audited. Use at your individual danger—evaluation the code, take a look at safely, and apply correct safeguards.
🔒 Tip of the Week
Map Recognized Vulnerabilities Routinely Throughout Your Stack — Attackers usually use Home windows Scheduled Duties to remain hidden on methods. Some go a step additional by eradicating key registry values like SD (Safety Descriptor) or Index, making their duties invisible to frequent instruments like Job Scheduler, schtasks, and even Autoruns. These hidden duties nonetheless run within the background and can be utilized for persistence or malware supply.
To examine for seen duties, instruments like Autoruns (by Sysinternals) and TaskSchedulerView (by NirSoft) are nice beginning factors. They present lively duties and allow you to spot uncommon ones. However hidden duties require deeper digging. You should use PowerShell to scan the registry path HKLMSOFTWAREMicrosoftWindows NTCurrentVersionScheduleTaskCacheTree and search for duties with lacking SD values.
For extra superior checks, use Sysmon to trace adjustments within the TaskCache registry and ProcMon to observe registry exercise in actual time. Search for suspicious activity names, lacking values, or duties with an Index of 0. Additionally, set alerts for Occasion ID 4698, which logs new scheduled activity creation.
In brief: use each visible instruments and registry checks to uncover hidden scheduled duties. Common scans, baseline comparisons, and fundamental alerting might help catch threats early—earlier than they do injury.
Conclusion
What’s turning into clearer every week is that attacker sophistication is not the exception—it is the baseline. AI-driven reconnaissance, credential abuse, and sign mimicry are not superior—they’re routine.
And as coordination gaps persist throughout security groups, the boundary between low-level noise and high-impact intrusions continues to blur. The end result is not only a sooner compromise—it is a deeper erosion of belief. If belief was as soon as a energy, it is now a floor that attackers exploit.




