Over 1,500 Android units have been contaminated by a brand new pressure of Android banking malware known as ToxicPanda that enables risk actors to conduct fraudulent banking transactions.
“ToxicPanda’s essential objective is to provoke cash transfers from compromised units by way of account takeover (ATO) utilizing a well known method known as on-device fraud (ODF),” Cleafy researchers Michele Roviello, Alessandro Strino, and Federico Valentini stated in a Monday evaluation.
“It goals to bypass financial institution countermeasures used to implement customers’ id verification and authentication, mixed with behavioral detection strategies utilized by banks to determine suspicious cash transfers.”
ToxicPanda is believed to be the work of a Chinese language-speaking risk actor, with the malware sharing foundational similarities with one other Android malware dubbed TgToxic, which might steal credentials and funds from crypto wallets. TgToxic was documented by Pattern Micro in early 2023.

A majority of the compromises have been reported in Italy (56.8%), adopted by Portugal (18.7%), Hong Kong (4.6%), Spain (3.9%), and Peru (3.4%), marking a uncommon occasion of a Chinese language risk actor orchestrating a fraudulent scheme to focus on retail banking customers in Europe and Latin America.
The banking trojan additionally seems to be in its nascent levels. Evaluation exhibits that it is a stripped-down model of its ancestor, eradicating Automated Switch System (ATS), Easyclick, and obfuscation routines, whereas additionally introducing 33 new instructions of its personal to reap a variety of knowledge.
As well as, as many as 61 instructions have been discovered to be widespread to each TgToxic and ToxicPanda, indicating that the identical risk actor or their shut associates are behind the brand new malware household.
“Whereas it shares some bot command similarities with the TgToxic household, the code diverges significantly from its authentic supply,” the researchers stated. “Many capabilities attribute of TgToxic are notably absent, and a few instructions seem as placeholders with out actual implementation.”

The malware masquerades as in style apps like Google Chrome, Visa, and 99 Speedmart, and is distributed by way of counterfeit pages mimicking app retailer itemizing pages. It is at the moment not identified how these hyperlinks are propagated and in the event that they contain malvertising or smishing strategies.
As soon as put in by way of sideloading, ToxicPanda abuses Android’s accessibility providers to achieve elevated permissions, manipulate consumer inputs, and seize knowledge from different apps. It could additionally intercept one-time passwords (OTPs) despatched by way of SMS or generated utilizing authenticator apps, thus enabling the risk actors to bypass two-factor authentication (2FA) protections and full fraudulent transactions.
The core performance of the malware, in addition to its means to reap info, is to allow attackers to remotely management the compromised machine and carry out what’s known as ODF, which makes it doable to provoke unauthorized cash transfers with out the sufferer’s information.
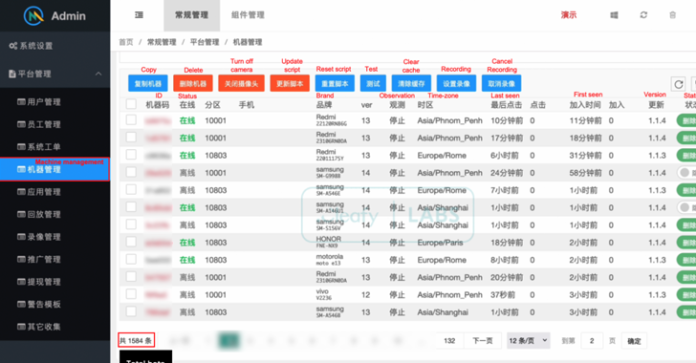
Cleafy stated it was in a position to acquire entry to ToxicPanda’s command-and-control (C2) panel, a graphical interface introduced in Chinese language that enables the operators to view the checklist of sufferer units, together with the mannequin info, and placement, and take away them from the bonnet. Moreover, the panel serves as a conduit to request real-time distant entry to any of the units for conducting ODF.

“ToxicPanda must display extra superior and distinctive capabilities that might complicate its evaluation,” the researchers stated. “Nonetheless, artifacts resembling logging info, useless code, and debugging recordsdata recommend that the malware might both be in its early levels of growth or present process intensive code refactoring—significantly given its similarities with TGToxic.”
The event comes as a gaggle of researchers from the Georgia Institute of Know-how, German Worldwide College, and Kyung Hee College detailed a backend malware evaluation service known as DVa – brief for Detector of Sufferer-specific Accessibility – to flag malware exploiting accessibility options on Android units.
“Utilizing dynamic execution traces, DVa additional makes use of an abuse-vector-guided symbolic execution technique to determine and attribute abuse routines to victims,” they stated. “Lastly, DVa detects [accessibility]-empowered persistence mechanisms to grasp how malware obstructs authorized queries or removing makes an attempt.”