Mandiant security analysts warn of a worrying new development of risk actors demonstrating a greater functionality to find and exploit zero-day vulnerabilities in software program.
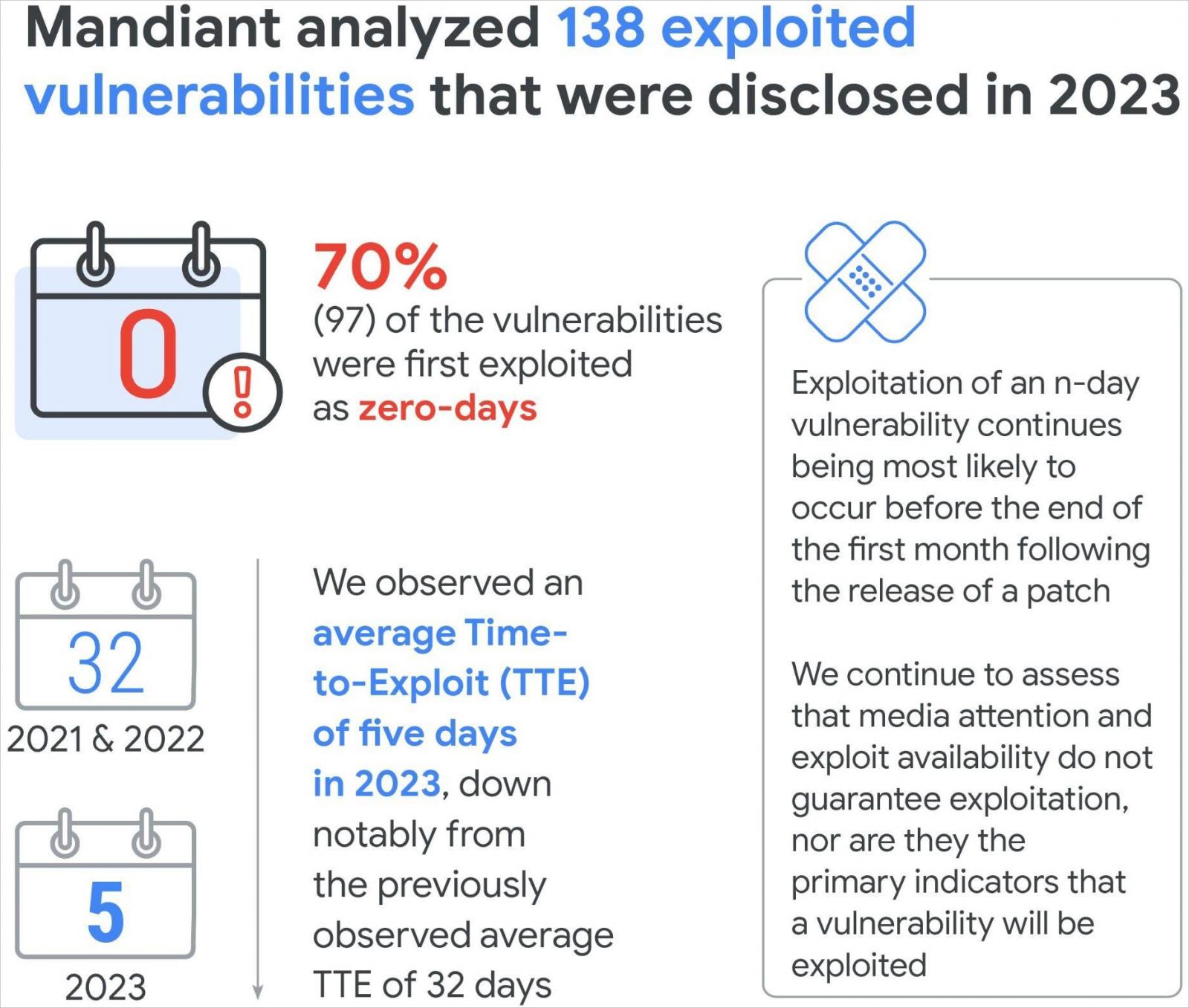
Particularly, of the 138 vulnerabilities disclosed as actively exploited in 2023, Mandiant says 97 (70.3%) had been leveraged as zero-days.
Because of this risk actors exploited the issues in assaults earlier than the impacted distributors knew of the bugs existence or had been in a position to patch them.
From 2020 till 2022, the ratio between n-days (fastened flaws) and zero-days (no repair obtainable) remained comparatively regular at 4:6, however in 2023, the ratio shifted to three:7.
Google explains that this isn’t as a consequence of a drop within the variety of n-days exploited within the wild however reasonably a rise in zero-day exploitation and the improved potential of security distributors to detect it.
This elevated malicious exercise and diversification in focused merchandise can be mirrored within the variety of distributors impacted by actively exploited flaws, which has elevated in 2023 to a file 56, up from 44 in 2022 and better than the earlier file of 48 distributors in 2021.
Response occasions getting tighter
One other important development was recorded relating to the time taken to take advantage of (TTE) a newly disclosed (n-day or 0-day) flaw, which has now dropped to only 5 days.
For comparability, in 2018-2019, TTE was 63 days, and in 2021-2022, TTE was 32 days. This gave system directors loads of time to plan the appliance of patches or implement mitigations to safe impacted programs.
Nonetheless, with the TTE now falling to five days, methods like community segmentation, real-time detection, and pressing patch prioritization turn out to be much more important.
On a associated word, Google doesn’t see a correlation between the disclosure of exploits and TTE.
In 2023, 75% of exploits had been made public earlier than exploitation within the wild had began, and 25% had been launched after hackers had been already leveraging the issues.
Two examples highlighted within the report back to showcase that there is no constant relationship between public exploit availability and malicious exercise are CVE-2023-28121 (WordPress plugin) and CVE-2023-27997 (Fortinet FortiOS).
.jpg)
Supply: Google
Within the first case, exploitation began three months after disclosure and ten days after a proof-of-concept was printed.
Within the FortiOS case, the flaw was weaponized nearly instantly in public exploits, however the first malicious exploitation occasion was recorded 4 months later.
Problem of exploitation, risk actor motivation, goal worth, and general assault complexity all play a job in TTE, and a direct or remoted correlation with PoC availability is flawed based on Google.




