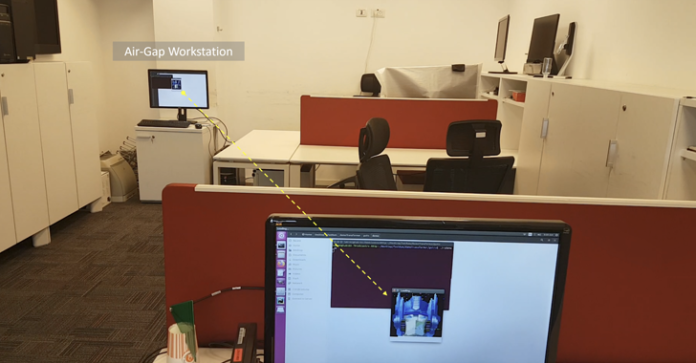
A novel side-channel assault has been discovered to leverage radio indicators emanated by a tool’s random entry reminiscence (RAM) as an information exfiltration mechanism, posing a menace to air-gapped networks.
The approach has been codenamed RAMBO by Dr. Mordechai Guri, the pinnacle of the Offensive Cyber Analysis Lab within the Division of Software program and Data Methods Engineering on the Ben Gurion College of the Negev in Israel.
“Utilizing software-generated radio indicators, malware can encode delicate data akin to recordsdata, photos, keylogging, biometric data, and encryption keys,” Dr. Guri stated in a newly revealed analysis paper.
“With software-defined radio (SDR) {hardware}, and a easy off-the-shelf antenna, an attacker can intercept transmitted uncooked radio indicators from a distance. The indicators can then be decoded and translated again into binary data.”

Through the years, Dr. Guri has concocted numerous mechanisms to extract confidential knowledge from offline networks by making the most of Serial ATA cables (SATAn), MEMS gyroscope (GAIROSCOPE), LEDs on community interface playing cards (ETHERLED), and dynamic energy consumption (COVID-bit).
A few of the different unconventional approaches devised by the researcher entail leaking knowledge from air-gapped networks by way of covert acoustic indicators generated by graphics processing unit (GPU) followers (GPU-FAN), (extremely)sonic waves produced by built-in motherboard buzzers (EL-GRILLO), and even printer show panels and standing LEDs (PrinterLeak).
Final 12 months, Guri additionally demonstrated AirKeyLogger, a hardwareless radio frequency keylogging assault that weaponizes radio emissions from a pc’s energy provide to exfiltrate real-time keystroke knowledge to a distant attacker.
“To leak confidential knowledge, the processor’s working frequencies are manipulated to generate a sample of electromagnetic emissions from the ability unit modulated by keystrokes,” Guri famous within the examine. “The keystroke data will be acquired at distances of a number of meters away by way of an RF receiver or a smartphone with a easy antenna.”
As at all times with assaults of this type, it requires the air-gapped community to be first compromised via different means – akin to a rogue insider, poisoned USB drives, or a provide chain assault – thereby permitting the malware to set off the covert knowledge exfiltration channel.
RAMBO is not any exception in that the malware is used to govern RAM such that it could possibly generate radio indicators at clock frequencies, that are then encoded utilizing Manchester encoding and transmitted in order to be acquired from a distance away.
The encoded knowledge can embody keystrokes, paperwork, and biometric data. An attacker on the opposite finish can then leverage SDR to obtain the electromagnetic indicators, demodulate and decode the info, and retrieve the exfiltrated data.

“The malware makes use of electromagnetic emissions from the RAM to modulate the knowledge and transmit it outward,” Dr. Guri stated. “A distant attacker with a radio receiver and antenna can obtain the knowledge, demodulate it, and decode it into its authentic binary or textual illustration.”
The approach could possibly be used to leak knowledge from air-gapped computer systems operating Intel i7 3.6GHz CPUs and 16 GB RAM at 1,000 bits per second, the analysis discovered, with keystrokes being exfiltrated in real-time with 16 bits per key.
“A 4096-bit RSA encryption key will be exfiltrated at 41.96 sec at a low pace and 4.096 bits at a excessive pace,” Dr. Guri stated. “Biometric data, small recordsdata (.jpg), and small paperwork (.txt and .docx) require 400 seconds on the low pace to a couple seconds on the quick speeds.”
“This means that the RAMBO covert channel can be utilized to leak comparatively temporary data over a brief interval.”
Countermeasures to dam the assault embody implementing “red-black” zone restrictions for data switch, utilizing an intrusion detection system (IDS), monitoring hypervisor-level reminiscence entry, utilizing radio jammers to dam wi-fi communications, and utilizing a Faraday cage.