Cyber assaults involving the DarkGate malware-as-a-service (MaaS) operation have shifted away from AutoIt scripts to an AutoHotkey mechanism to ship the final levels, underscoring continued efforts on the a part of the risk actors to repeatedly keep forward of the detection curve.
The updates have been noticed in model 6 of DarkGate launched in March 2024 by its developer RastaFarEye, who has been promoting this system on a subscription foundation to as many as 30 clients. The malware has been lively since no less than 2018.
A totally-featured distant entry trojan (RAT), DarkGate is supplied with command-and-control (C2) and rootkit capabilities, and incorporates varied modules for credential theft, keylogging, display screen capturing, and distant desktop.

“DarkGate campaigns are likely to adapt actually quick, modifying totally different parts to attempt to keep off security options,” Trellix security researcher Ernesto Fernández Provecho stated in a Monday evaluation. “That is the primary time we discover DarkGate utilizing AutoHotKey, a not so frequent scripting interpreter, to launch DarkGate.”
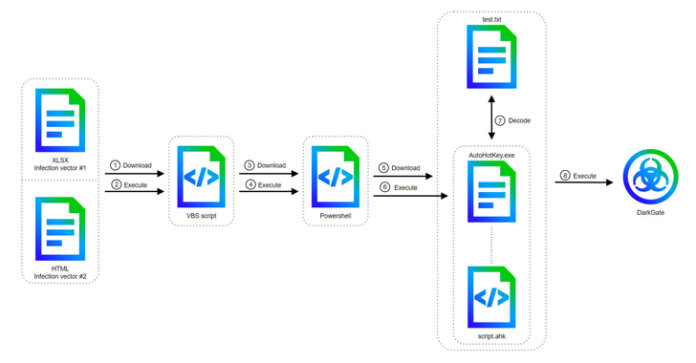
It is value noting that DarkGate’s change to AutoHotKey was first documented by McAfee Labs in late April 2024, with assault chains leveraging security flaws corresponding to CVE-2023-36025 and CVE-2024-21412 to bypass Microsoft Defender SmartScreen protections utilizing a Microsoft Excel or an HTML attachment in phishing emails.

Alternate strategies have been discovered to leverage Excel recordsdata with embedded macros as a conduit to execute a Visible Fundamental Script file that is chargeable for invoking PowerShell instructions to finally launch an AutoHotKey script, which, in flip, retrieves and decodes the DarkGate payload from a textual content file.
The most recent model of DarkGate packs in substantial upgrades to its configuration, evasion methods, and the checklist of supported instructions, which now consists of audio recording, mouse management, and keyboard administration options.
“Model 6 not solely consists of new instructions, but in addition lacks a few of them from earlier variations, just like the privilege escalation, the cryptomining, or the hVNC (Hidden Digital Community Computing) ones,” Fernández Provecho stated, including it could be an effort to chop out options that might allow detection.

“Furthermore, since DarkGate is offered to a small group of individuals, additionally it is potential that the shoppers weren’t thinking about these options, forcing RastaFarEye to take away them.”
The disclosure comes as cyber criminals have been discovered abusing Docusign by promoting legitimate-looking customizable phishing templates on underground boards, turning the service right into a fertile floor for phishers seeking to steal credentials for phishing and enterprise e-mail compromise (BEC) scams.
“These fraudulent emails, meticulously designed to imitate authentic doc signing requests, lure unsuspecting recipients into clicking malicious hyperlinks or divulging delicate data,” Irregular Safety stated.