Cybersecurity researchers have uncovered an “implementation vulnerability” that has made it potential to reconstruct encryption keys and decrypt information locked by Rhysida ransomware.
The findings had been revealed final week by a gaggle of researchers from Kookmin College and the Korea Web and Safety Company (KISA).
“By a complete evaluation of Rhysida Ransomware, we recognized an implementation vulnerability, enabling us to regenerate the encryption key utilized by the malware,” the researchers mentioned.
The event marks the primary profitable decryption of the ransomware pressure, which first made its look in Could 2023. A restoration device is being distributed by means of KISA.
The examine can also be the newest to realize information decryption by exploiting implementation vulnerabilities in ransomware, after Magniber v2, Ragnar Locker, Avaddon, and Hive.
Rhysida, which is understood to share overlaps with one other ransomware crew known as Vice Society, leverages a tactic often known as double extortion to use stress on victims into paying up by threatening to launch their stolen information.
An advisory revealed by the U.S. authorities in November 2023 known as out the menace actors for staging opportunistic assaults focusing on training, manufacturing, info know-how, and authorities sectors.
A radical examination of the ransomware’s internal workings has revealed its use of LibTomCrypt for encryption in addition to parallel processing to hurry up the method. It has additionally been discovered to implement intermittent encryption (aka partial encryption) to evade detection by security options.
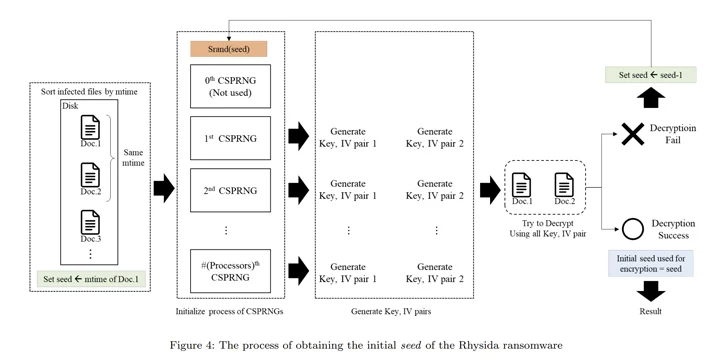
“Rhysida ransomware makes use of a cryptographically safe pseudo-random quantity generator (CSPRNG) to generate the encryption key,” the researchers mentioned. “This generator makes use of a cryptographically safe algorithm to generate random numbers.”
Particularly, the CSPRNG is predicated on the ChaCha20 algorithm supplied by the LibTomCrypt library, with the random quantity generated additionally correlated to the time at which Rhysida ransomware is working.
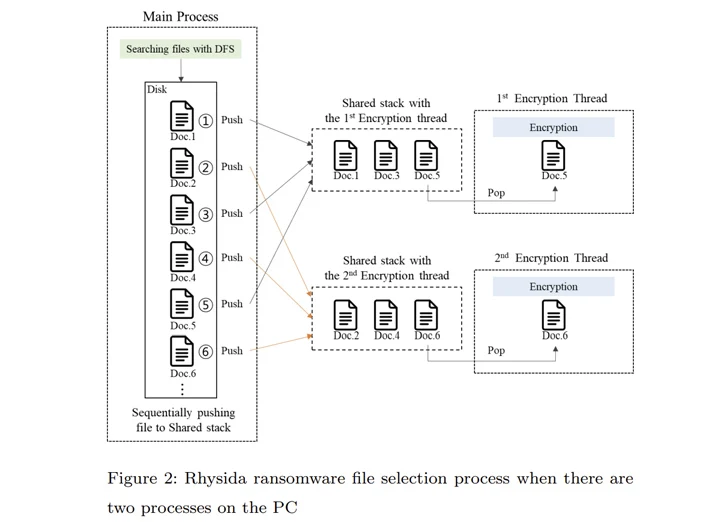
That is not all. The principle strategy of Rhysida ransomware compiles an inventory of information to be encrypted. This record is subsequently referenced by numerous threads created to concurrently encrypt the information in a selected order.
“Within the encryption strategy of the Rhysida ransomware, the encryption thread generates 80 bytes of random numbers when encrypting a single file,” the researchers famous. “Of those, the primary 48 bytes are used because the encryption key and the [initialization vector].”
Utilizing these observations as reference factors, the researchers mentioned they had been in a position to retrieve the preliminary seed for decrypting the ransomware, decide the “randomized” order during which the information had been encrypted, and in the end get better the information with out having to pay a ransom.
“Though these research have a restricted scope, it is very important acknowledge that sure ransomwares […] will be efficiently decrypted,” the researchers concluded.




