The Iranian menace actor generally known as Tortoiseshell has been attributed to a brand new wave of watering gap assaults which might be designed to deploy a malware dubbed IMAPLoader.
“IMAPLoader is a .NET malware that has the power to fingerprint sufferer programs utilizing native Home windows utilities and acts as a downloader for additional payloads,” the PwC Menace Intelligence mentioned in a Wednesday evaluation.
“It makes use of electronic mail as a [command-and-control] channel and is ready to execute payloads extracted from electronic mail attachments and is executed by way of new service deployments.”
Energetic since at the least 2018, Tortoiseshell has a historical past of utilizing strategic web site compromises as a ploy to facilitate the distribution of malware. Earlier this Could, ClearSky linked the group to the breach of eight web sites related to delivery, logistics, and monetary providers firms in Israel.
The menace actor is aligned with the Islamic Revolutionary Guard Corps (IRGC) and can also be tracked by the broader cybersecurity group below the names Crimson Sandstorm (beforehand Curium), Imperial Kitten, TA456, and Yellow Liderc.
The newest set of assaults between 2022 and 2023 entails embedding malicious JavaScript in compromised reputable web sites to assemble extra particulars in regards to the guests, together with their location, system info, and time of visits.
These intrusions centered totally on the maritime, delivery and logistics sectors within the Mediterranean, in some instances resulting in the deployment of IMAPLoader as a follow-on payload ought to the sufferer be deemed a high-value goal.
IMAPLoader is claimed to be a substitute to a Python-based IMAP implant Tortoiseshell beforehand utilized in late 2021 and early 2022, owing to the similarities within the performance.
The malware acts as a downloader for next-stage payloads by querying hard-coded IMAP electronic mail accounts, particularly checking a mailbox folder misspelled as “Recive” to retrieve the executables from the message attachments.
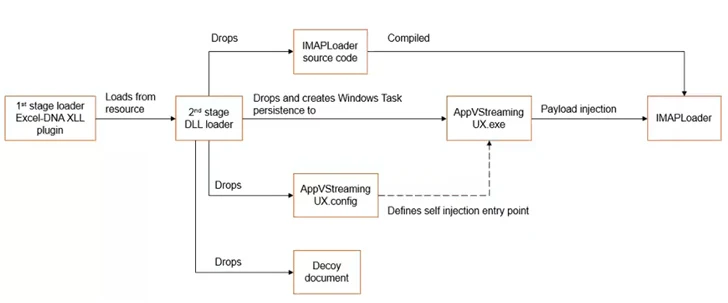
In an alternate assault chain, a Microsoft Excel decoy doc is used as an preliminary vector to kick-start a multi-stage course of to ship and execute IMAPLoader, indicating that the menace actor is utilizing quite a lot of ways and strategies to appreciate its strategic targets.
PwC mentioned it additionally found phishing websites created by Tortoiseshell, a few of that are aimed on the journey and hospitality sectors inside Europe, to conduct credential harvesting utilizing pretend Microsoft sign-in pages.
“This menace actor stays an energetic and protracted menace to many industries and international locations, together with the maritime, delivery, and logistics sectors inside the Mediterranean; nuclear, aerospace, and protection industries within the U.S. and Europe; and IT managed service suppliers within the Center East,” PwC mentioned.




