1000’s of Openfire XMPP servers are unpatched in opposition to a lately disclosed high-severity flaw and are inclined to a brand new exploit, in keeping with a brand new report from VulnCheck.
Tracked as CVE-2023-32315 (CVSS rating: 7.5), the vulnerability pertains to a path traversal vulnerability in Openfire’s administrative console that might allow an unauthenticated attacker to entry in any other case restricted pages reserved for privileged customers.
It impacts all variations of the software program launched since April 2015, beginning with model 3.10.0. It was remediated by its developer, Ignite Realtime, earlier this Could with the discharge of variations 4.6.8, 4.7.5, and 4.8.0.
“Path traversal protections had been already in place to guard in opposition to precisely this sort of assault, however did not defend in opposition to sure non-standard URL encoding for UTF-16 characters that weren’t supported by the embedded net server that was in use on the time,” the maintainers stated in an in depth advisory.
“A later improve of the embedded net server included help for non-standard URL encoding of UTF-16 characters. The trail traversal protections in place in Openfire weren’t up to date to incorporate safety in opposition to this new encoding.”
In consequence, a menace actor may abuse this weak spot to bypass authentication necessities for admin console pages. The vulnerability has since come underneath energetic exploitation within the wild, together with by attackers related to the Kinsing (aka Cash Libra) crypto botnet malware.
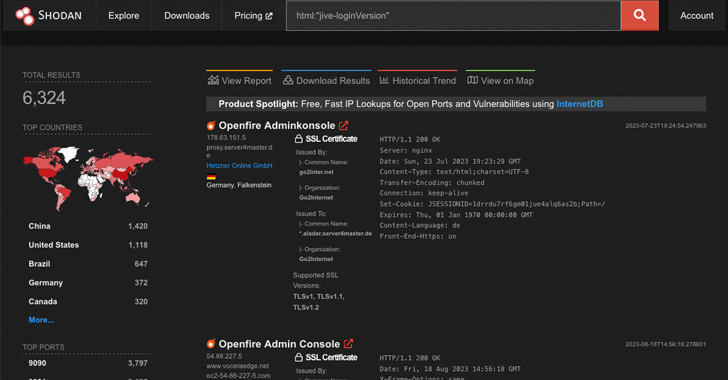
A Shodan scan performed by the cybersecurity agency reveals that of greater than 6,300 Openfire servers accessible over the web, roughly 50% of them are working affected variations of the open-source XMPP answer.
Whereas public exploits have leveraged the vulnerability to create an administrative person, log in, after which add a plugin to realize code execution, VulnCheck stated it is potential to take action with out having to create an admin account, making it extra stealthy and interesting for menace actors.
Elaborating on the modus operandi of the present exploits, security researcher Jacob Baines stated they contain “creating an admin person to realize entry to the Openfire Plugins interface.”
“The plugin system permits directors so as to add, roughly, arbitrary performance to Openfire by way of uploaded Java JARs. That is, very clearly, a spot to transition from authentication bypass to distant code execution.”
The improved, much less noisy methodology devised by VulnCheck, however, employs a user-less strategy that extracts the JSESSIONID and CSRF token by accessing a web page known as ‘plugin-admin.jsp’ after which importing the JAR plugin by way of a POST request.
“With out authentication, the plugin is accepted and put in,” Baines stated. “The net shell can then be accessed, with out authentication, utilizing the traversal.”
“This strategy retains login makes an attempt out of the security audit log and prevents the ‘uploaded plugin’ notification from being recorded. That is a fairly large deal as a result of it leaves no proof within the security audit log.”
The one tell-tale indicators that one thing malicious is afoot are the logs captured within the openfire.log file, which an adversary may delete through the use of CVE-2023-32315, the corporate stated.
With the vulnerability already being exploited in real-world assaults, it is beneficial that customers transfer rapidly to replace to the most recent variations to safe in opposition to potential threats.




