A 7-Zip vulnerability permitting attackers to bypass the Mark of the Net (MotW) Home windows security characteristic was exploited by Russian hackers as a zero-day since September 2024.
In accordance with Pattern Micro researchers, the flaw was utilized in SmokeLoader malware campaigns focusing on the Ukrainian authorities and personal organizations within the nation.
The Mark of the Net is a Home windows security characteristic designed to warn customers that the file they’re about to execute comes from untrusted sources, requesting a affirmation step by way of a further immediate. Bypassing MoTW permits malicious information to run on the sufferer’s machine with no warning.
When downloading paperwork and executables from the net or acquired as an e-mail attachment, Home windows provides a particular ‘Zone.Id’ alternate knowledge stream known as the Mark-of-the-Net (MoTW) to the file.
When trying to open a downloaded file, Home windows will verify if a MoTW exists and, if that’s the case, show further warnings to the person, asking if they’re certain they want to run the file. Equally, when opening a doc in Phrase or Excel with a MoTW flag, Microsoft Workplace will generate further warnings and switch off macros.
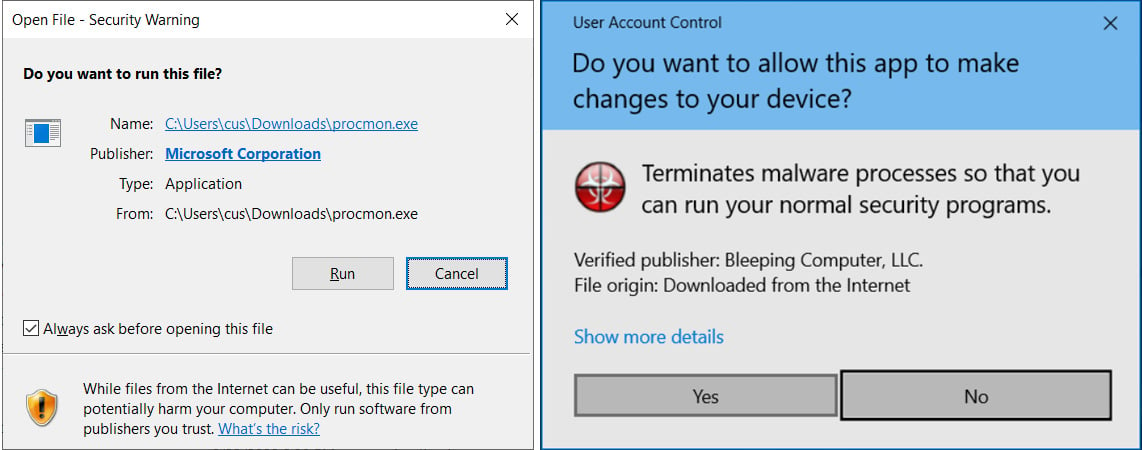
Supply: BleepingComputer
Because the Mark of the Net security options forestall harmful information from routinely working, risk actors generally try to seek out MoTW bypasses so their information routinely run and execute.
For years, cybersecurity researchers requested 7-Zip add assist for the Mark of the Net, nevertheless it was solely in 2022 that assist for the characteristic was lastly added.
MoTW bypasses exploited in assaults
Pattern Micro’s Zero Day Initiative (ZDI) workforce first found the flaw, now tracked as CVE-2025-0411, on September 25, 2024, observing it in assaults carried out by Russian risk actors.
Hackers leveraged CVE-2025-0411 utilizing double archived information (an archive inside an archive) to take advantage of an absence of inheritance of the MoTW flag, leading to malicious file execution with out triggering warnings.
The specifically crafted archive information had been despatched to targets by way of phishing emails from compromised Ukrainian authorities accounts to bypass security filters and seem reliable.
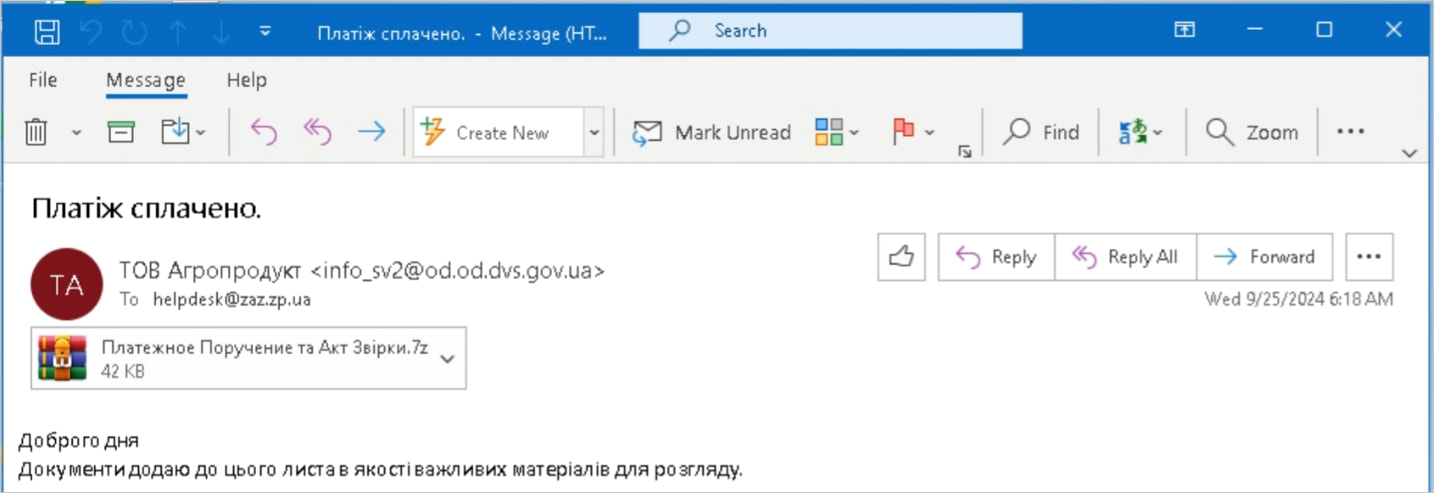
Supply: Pattern Micro
Using homoglyph methods, the attackers hid their payloads throughout the 7-Zip information, making them seem innocent Phrase or PDF paperwork.
Though opening the father or mother archive does propagate the MoTW flag, the CVE-2025-0411 flaw precipitated the flag to not propagate to the contents of the inside archive, permitting malicious scripts and executables to launch straight.
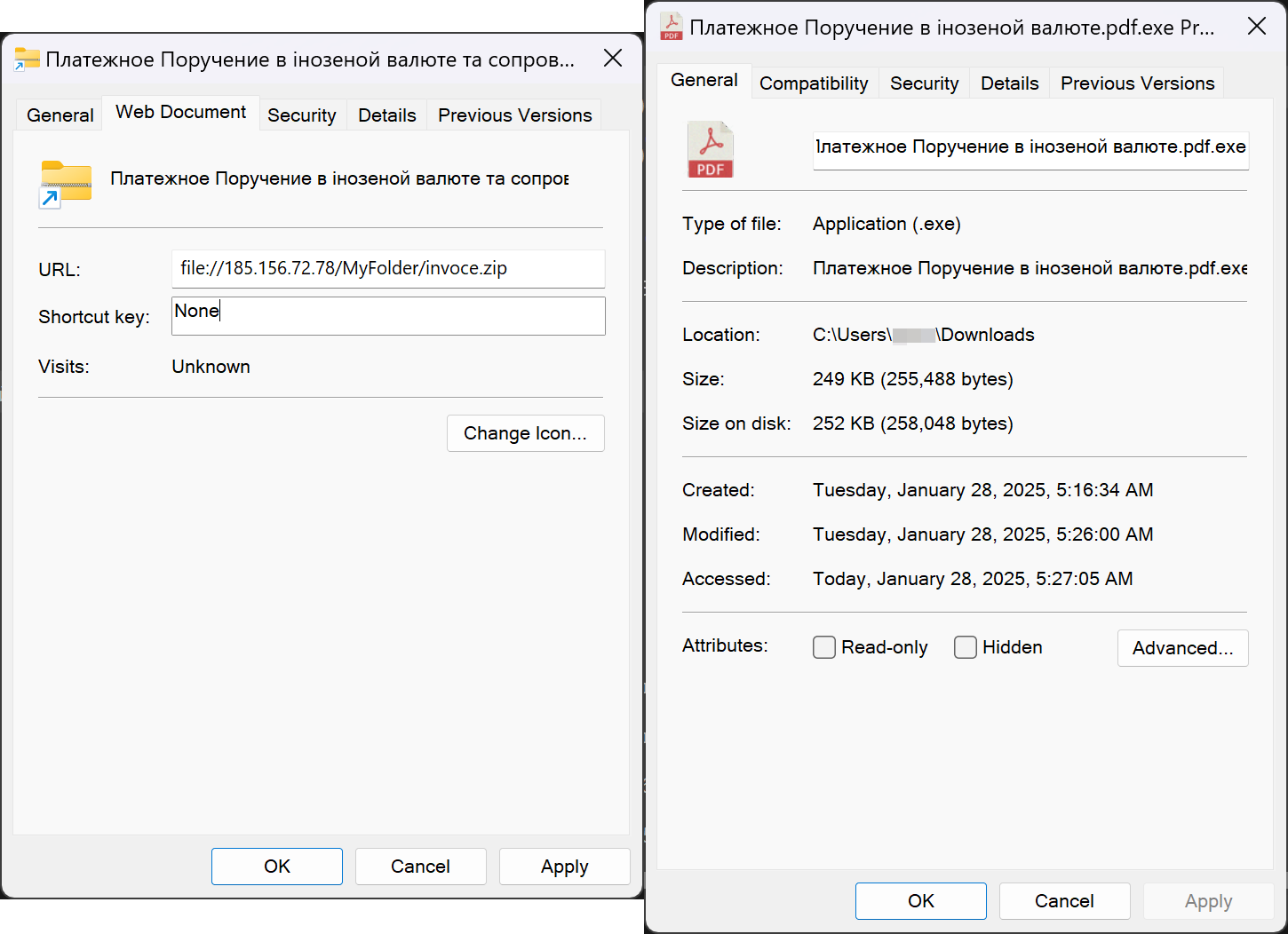
Supply: Pattern Micro
This final step triggers the SmokeLoader payload, a malware dropper used up to now to put in info-stealers, trojans, ransomware, or creating backdoors for persistent entry.
Pattern Micro says these assaults impacted the next organizations:
- State Govt Service of Ukraine (SES) – Ministry of Justice
- Zaporizhzhia Vehicle Constructing Plant (PrJSC ZAZ) – Vehicle, bus, and truck producer
- Kyivpastrans – Kyiv Public Transportation Service
- SEA Firm – Home equipment, electrical gear, and electronics producer
- Verkhovyna District State Administration – Ivano-Frankivsk oblast administration
- VUSA – Insurance coverage firm
- Dnipro Metropolis Regional Pharmacy – Regional pharmacy
- Kyivvodokanal – Kyiv Water Provide Firm
- Zalishchyky Metropolis Council – Metropolis council
Replace 7-Zip
Though the invention of the zero-day got here in September, it took Pattern Micro till October 1, 2024, to share a working proof-of-concept (PoC) exploit with the builders of 7-Zip.
The latter addressed the dangers by way of a patch applied in model 24.09, launched on November 30, 2024. Nonetheless, as 7-Zip doesn’t embody an auto-update characteristic, it’s common for 7-Zip customers to run outdated variations.
Subsequently, it’s strongly really helpful that customers obtain the most recent model to ensure they’re protected against this vulnerability.




