With Gartner just lately declaring that SOAR (security orchestration, automation, and response) is being phased out in favor of generative AI-based options, this text will discover intimately 4 key security automation use instances.
1. Enriching Indicators of Compromise (IoCs)
Indicators of compromise (IoCs), equivalent to suspicious IP addresses, domains, and file hashes, are important in figuring out and responding to security incidents.
Manually gathering details about these IoCs from numerous sources might be labor-intensive and decelerate the response course of.
Automating the enrichment of IoCs can tremendously improve the effectivity of your security operations.
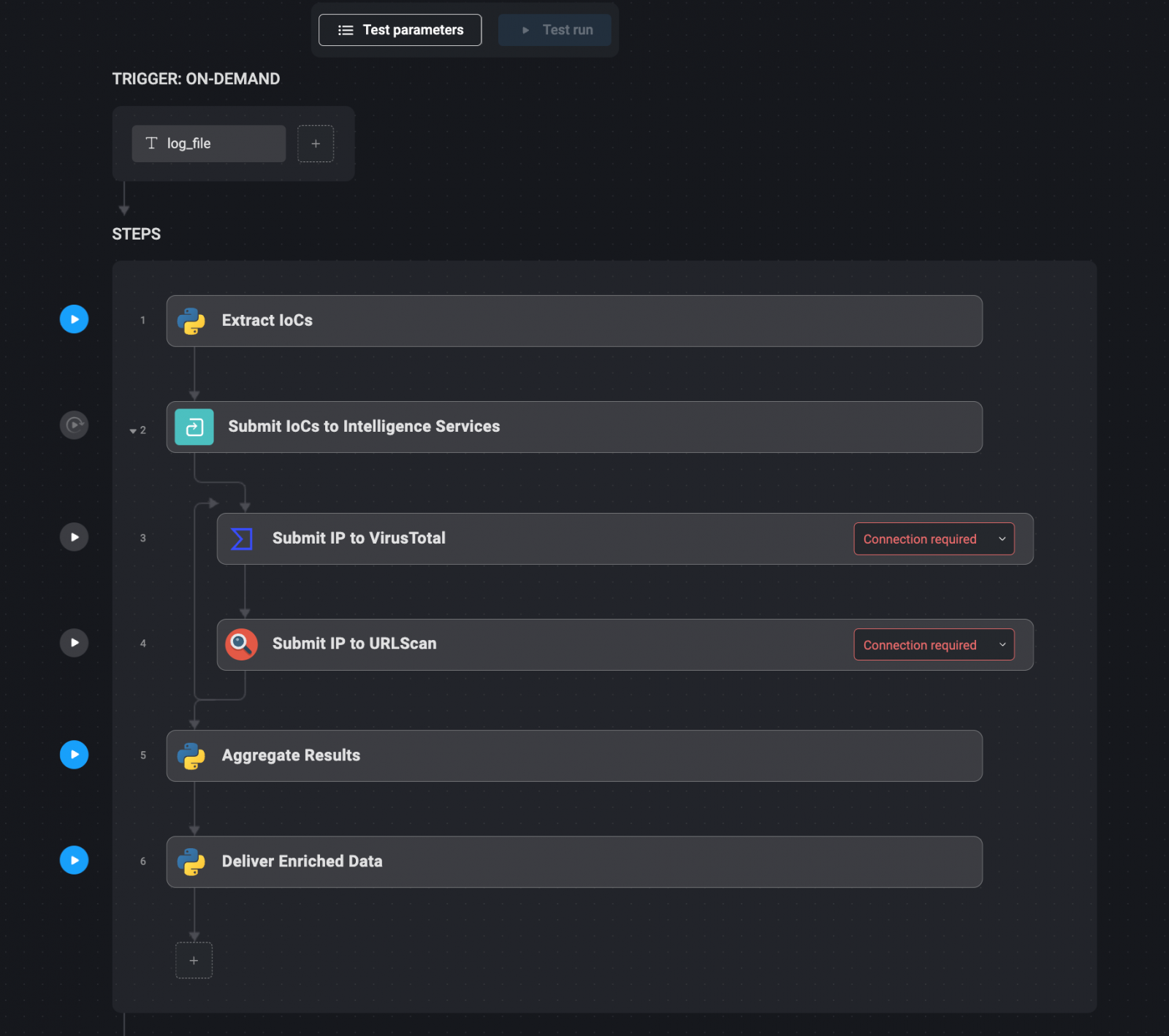
Automation workflow:
- Extract IoCs: Mechanically extract related IoCs from security logs or alerts utilizing textual content parsing instruments or different automated strategies.
- Submit IoCs to Intelligence Providers: As soon as extracted, the IoCs are mechanically submitted to varied menace intelligence companies, equivalent to VirusTotal, URLScan, and AlienVault, through their APIs. These companies can present further context, equivalent to whether or not the IP tackle has been related to recognized threats or if the area has been flagged for suspicious exercise.
- Mixture Outcomes: The outcomes from these intelligence companies are aggregated right into a single, complete report. This step ensures that every one related data is accessible in a single place, making it simpler for security analysts to evaluate the menace.
- Ship Enriched Data: The enriched IoC information is then delivered by way of communication channels like Slack, or instantly added to the related incident ticket inside the security administration system. This ensures that every one mandatory data is instantly accessible to those that want it.
2. Monitoring Your Exterior Attack Floor
The exterior assault floor of a company consists of all of the external-facing belongings that would probably be exploited by attackers.
These belongings embody domains, IP addresses, subdomains, uncovered companies, and extra.
Common monitoring of those belongings is essential for figuring out and mitigating potential vulnerabilities earlier than they’re exploited.
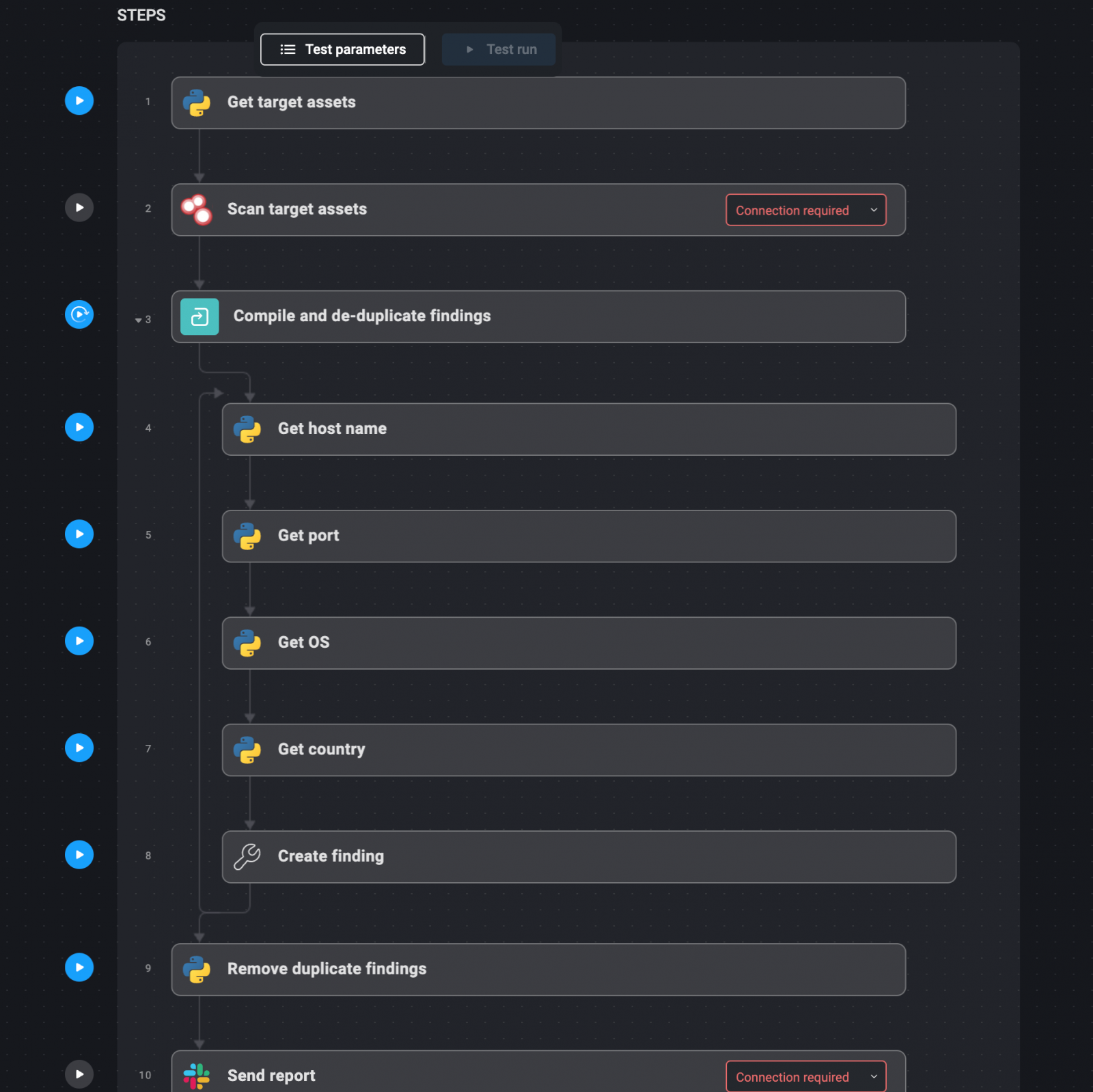
Automation workflow:
- Outline Goal Property: Begin by defining the domains and IP addresses that make up your exterior assault floor. These must be documented in a file that the automation system can reference.
- Automated Reconnaissance: Use instruments like Shodan to scan these belongings on a weekly or month-to-month foundation. Shodan may help establish open ports, uncovered companies, and different vulnerabilities.
- Compile and De-duplicate Findings: The outcomes from these scans are mechanically compiled right into a report. Any duplicate findings are eliminated to make sure that the report is concise and actionable.
- Ship Weekly Stories: The ultimate report is delivered through e-mail, Slack, or one other most well-liked communication channel. This report highlights new or modified belongings, potential vulnerabilities, and any redundant functions that will pose a danger.
3. Scanning for Internet Utility Vulnerabilities
Internet functions are frequent targets for attackers, making common vulnerability scans helpful for sustaining security.
Instruments like OWASP ZAP and Burp Suite automate the method of figuring out frequent vulnerabilities, together with outdated software program and misconfigurations.
These scans additionally detect enter validation vulnerabilities, serving to to safe internet functions.
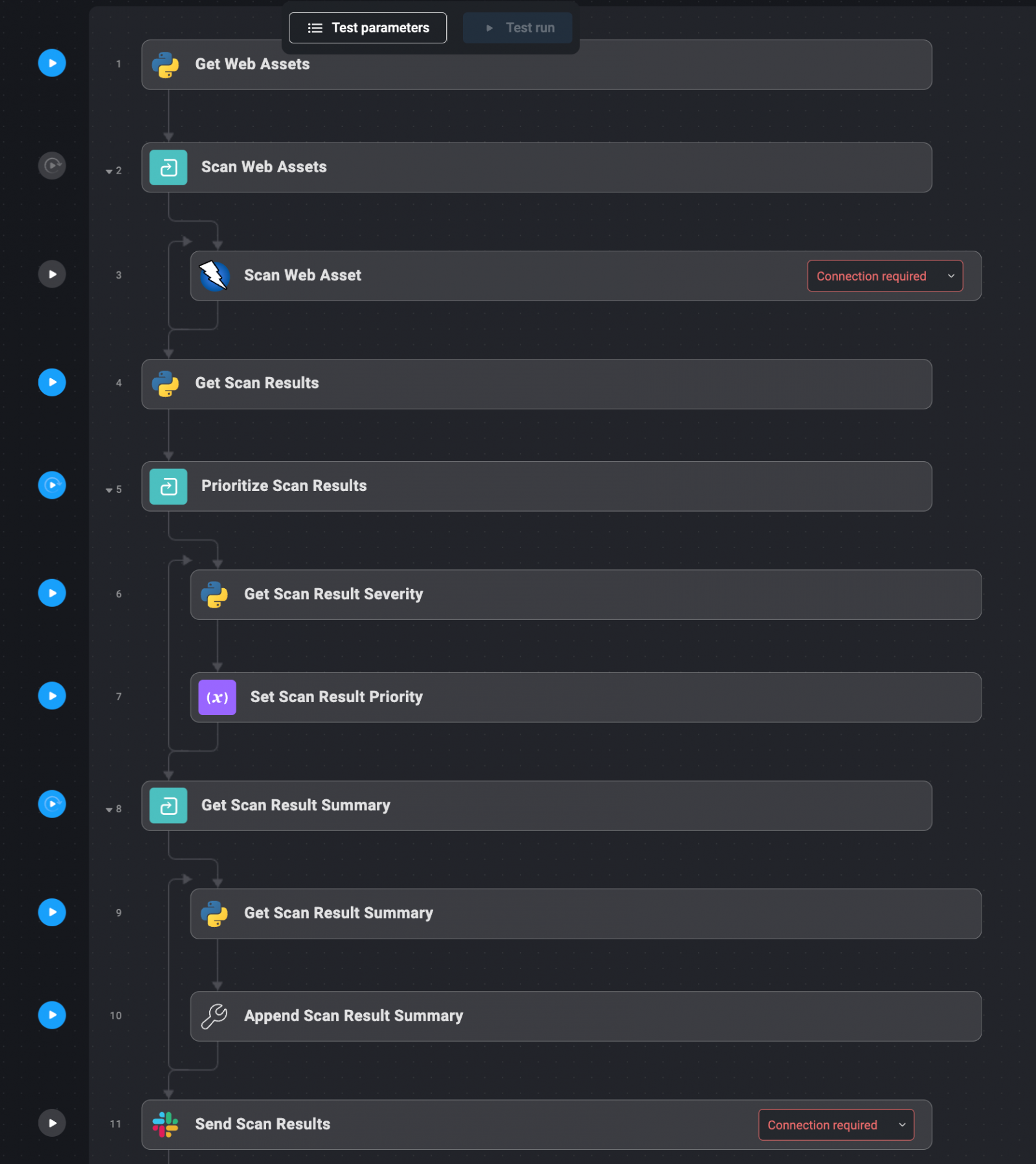
Automation workflow:
- Outline Internet Property: Start by itemizing all of the domains and IP addresses that host your group’s internet functions. These belongings must be documented in a file for simple reference by the automation system.
- Automated Vulnerability Scanning: The outlined internet belongings are mechanically despatched to scanning instruments like OWASP ZAP and Burp Suite. These instruments carry out complete scans to establish vulnerabilities, together with these which can be generally exploited by attackers.
- Gather and Prioritize Outcomes: The outcomes from the scans are mechanically collected and prioritized based mostly on the severity of the vulnerabilities detected. Essential/extreme vulnerabilities are highlighted for fast motion.
- Ship Outcomes: The prioritized outcomes are delivered to the related groups through Slack or as an enriched ticket inside the incident administration system. This ensures that the proper persons are notified of the vulnerabilities and may take applicable motion.
4. Monitoring E mail Addresses For Stolen Credentials
Monitoring for compromised credentials is a crucial facet of a company’s cybersecurity technique.
Have I Been Pwned (HIBP) is a extensively used service that aggregates information from numerous breaches to assist people and organizations decide if their credentials have been compromised.
Automating the method of checking HIBP for uncovered credentials may help organizations rapidly establish and reply to potential security incidents.
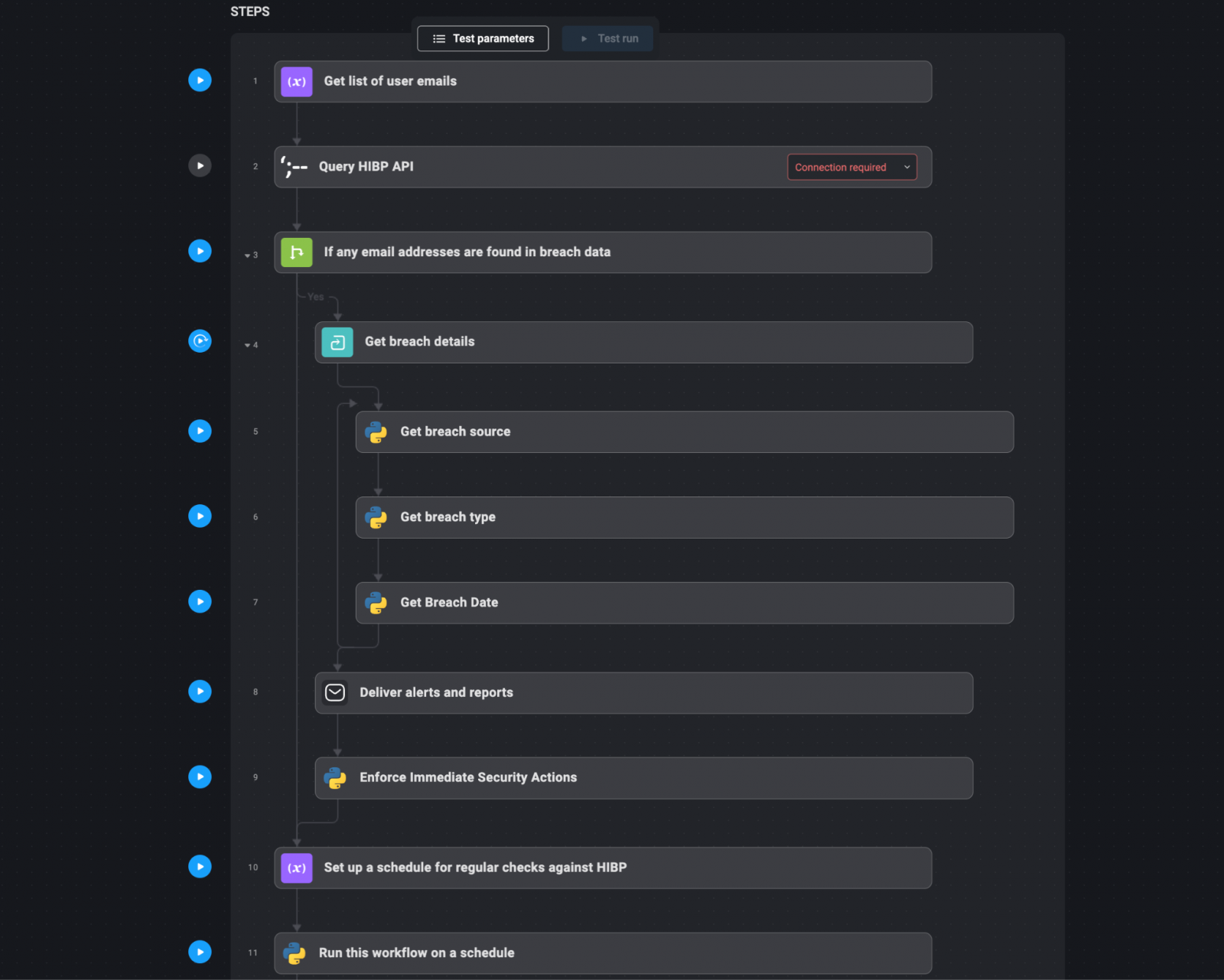
Automation workflow:
- Compile Consumer Emails and Domains: Create a listing of consumer e-mail addresses or domains that have to be monitored. This checklist ought to embody all related consumer accounts inside the group, particularly these with privileged entry.
- Question HIBP API: Mechanically question the HIBP API with the compiled checklist of e-mail addresses or domains. This step includes sending requests to HIBP to examine if any of the e-mail addresses have appeared in recognized data breaches.
- Mixture and Analyze Outcomes: Gather the responses from HIBP. If any e-mail addresses or domains are present in breach information, the main points of those breaches (such because the breach supply, sort of uncovered information, and date of the breach) are aggregated and analyzed.
- Ship Alerts and Stories: If compromised credentials are detected, mechanically generate an alert. This alert might be despatched through e-mail, Slack, or built-in into the group’s incident response system as a high-priority ticket. Embrace detailed details about the breach, such because the affected e-mail addresses, the character of the publicity, and beneficial actions (e.g., forcing password resets).
- Implement Fast Safety Actions: Primarily based on the severity of the breach, the system can mechanically implement security actions. For instance, it would set off a password reset for affected accounts, notify the customers concerned, and improve monitoring on accounts that have been compromised.
- Common Scheduled Checks: Arrange a schedule for normal checks in opposition to HIBP, equivalent to weekly or month-to-month queries. This ensures that the group stays conscious of any new breaches that may contain their credentials and may reply promptly.
Incessantly Requested Questions
Under we are going to reply some incessantly requested questions in regards to the automated workflows above and the way they may help in a sensible method.
- Don’t third-party companies provide automation workflows anyway?
Many companies present APIs that permit for automating components of the workflow, like fetching information. Nevertheless, constructing an end-to-end automated workflow sometimes requires coding and configurations. Replicating your entire workflow with scripts presents flexibility however is much less highly effective, as modifications may break it. Leveraging accessible APIs with a centralized automation platform supplies a secure, scalable answer. - Can’t we simply replicate this complete factor with bash scripts?
Sure, it’s doable to jot down Bash/PowerShell scripts to automate the security duties talked about within the article. Scripts provide flexibility that’s missing in handbook processes. Nevertheless, scripts require ongoing upkeep, and any modifications may break the workflow. They might additionally lack superior options like central administration, scheduling, alerting, and reporting, that are provided by devoted automation platforms like Blink Ops. A correct platform is extra dependable and environment friendly for advanced, long-running automation necessities. - How does automating IoC enrichment assist?
Automating IoC enrichment quickens the response course of by gathering menace intelligence on indicators like IPs, domains, and file hashes from a number of sources concurrently through APIs. This supplies security groups with a single complete report with the required context to evaluate threats rapidly, reasonably than spending time manually looking totally different sources. It improves effectivity and situational consciousness, enabling knowledgeable selections to be made rapidly.
Enhance Your Cybersecurity Posture With Blink Ops
Blink is an ROI pressure multiplier for security groups and enterprise leaders who need to rapidly and simply safe a variety of use instances, together with SOC and incident response, vulnerability administration, cloud security, identification and entry administration, and governance, danger, and compliance.
With 1000’s of automations within the Blink library and the power to customise workflows to suit your particular use case, Blink Ops can considerably enhance your security operations.
Get began with Blink Ops.
Sponsored and written by Blink Ops.




